0x00 本机环境 Apple系列的芯片性能好,风扇基本不转。折腾下Android>7的虚拟机环境,证书配置稍微复杂写。
MBP M2
镜像: Android API 33
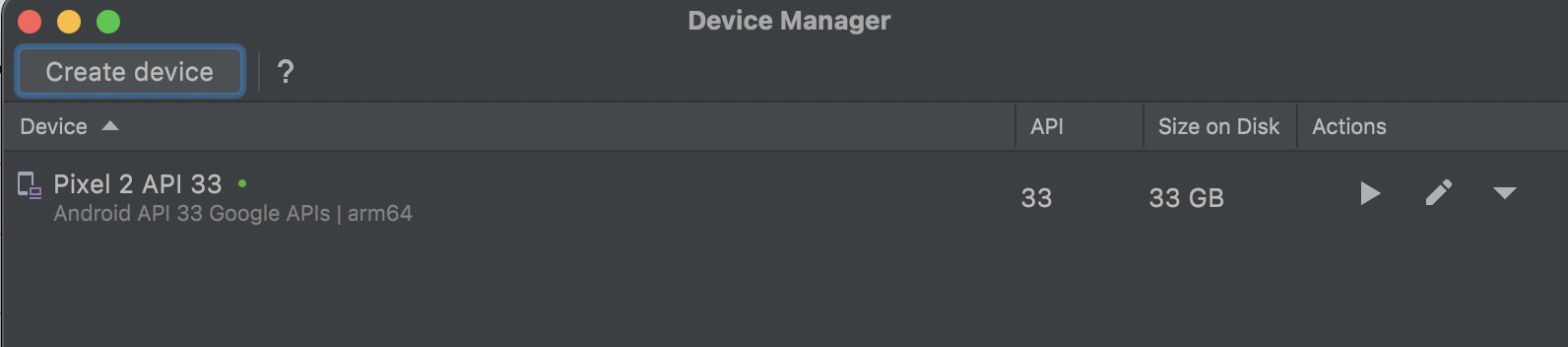
通过AVD创建Android API 33镜像的虚拟机:
有几点注意:
不能使用Google Play镜像,要用Google API镜像,不然无法root
不能安装x86_84 架构的镜像,不兼容: PANIC: Avd’s CPU Architecture ‘x86_64’ is not supported by the QEMU2 emulator on aarch64 host.
0x01 操作步骤 1.生成Burp证书:
1 2 3 4 openssl x509 -inform DER -in burp_ca_6.cer -out cacert_6.pem openssl x509 -inform PEM -subject_hash_old -in cacert_6.pem |head -1 9 a5ba575mv cacert_6.pem 9 a5ba575.0
2.启动模拟器,重载系统目录:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 ➜ ~ emulator -list-avds Pixel_3a_API_33_arm64-v8a ➜ ~ emulator -avd Pixel_3a_API_33_arm64-v8a -writable-system ➜ ~ adb root restarting adbd as root ➜ ~ adb remount Using overlayfs for /system Using overlayfs for /vendor Using overlayfs for /product Using overlayfs for /system_ext Now reboot your device for settings to take effect remount succeeded ➜ ~ adb shell emu64a:/ # mount -o rw,remount /system
3.push证书到系统目录
1 2 3 4 adb push 9 a5ba575.0 /sdcard/ Documents emu64a: /sdcard/ Documents # cp 9a5ba575.0 /system/etc/security/cacerts/ emu64a: /sdcard/ Documents # cd /system/etc/security/cacerts/ emu64a: /system/ etc/security/ cacerts # chmod 644 9a5ba575.0
4.赋权并设置不校验证书
1 2 3 chown root:root /system/etc/security/cacerts/9 a5ba575.0 adb shell avbctl disable -verification adb reboot
5.禁用IPv6
1 echo 1 > /proc/ sys/net/i pv6/conf/ wlan0/disable_ipv6
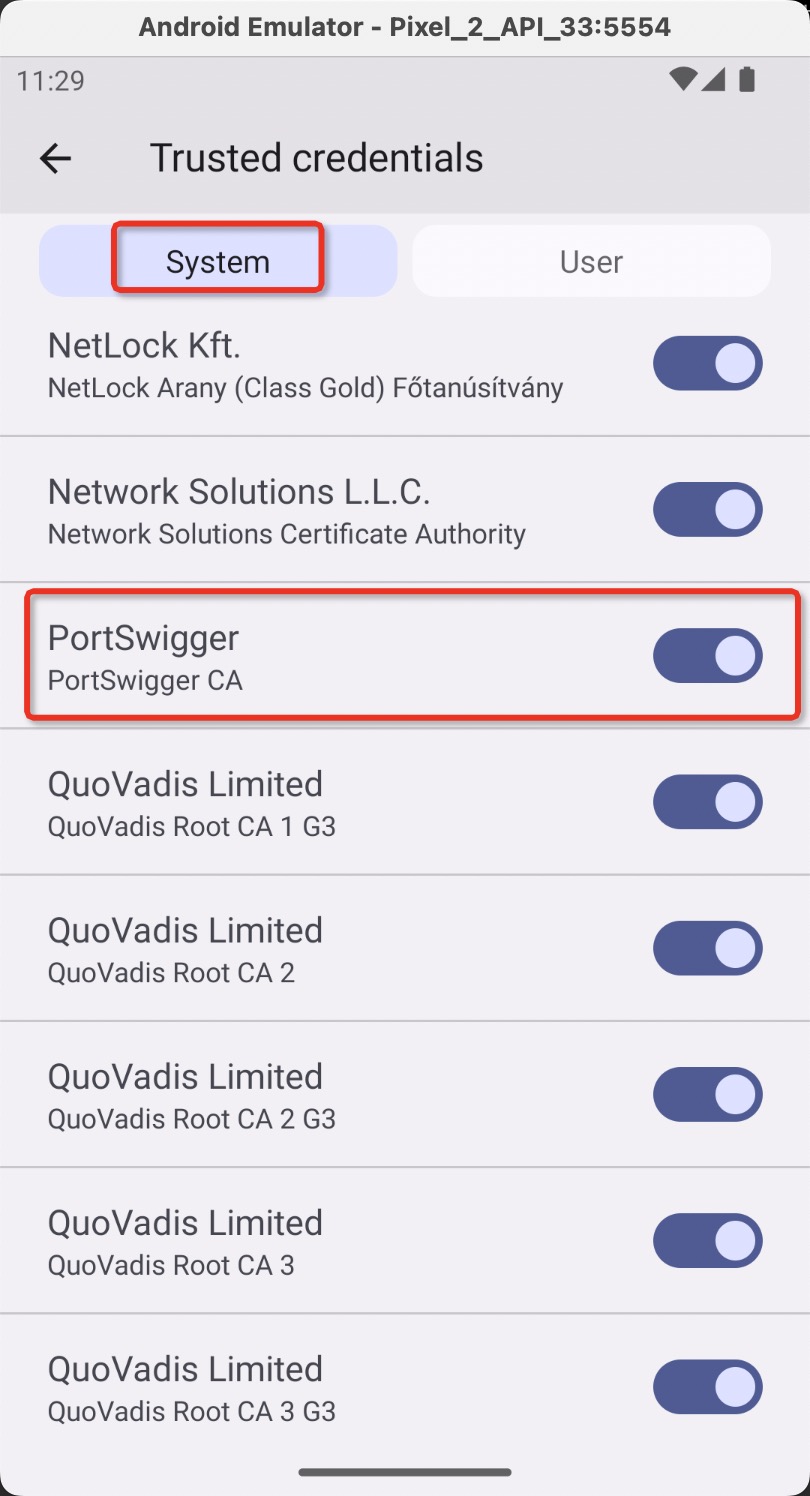
6.系统里面查看证书:
7.chrome最新版问题(Certificate Transparency)
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 # see https: //httptoolkit.tech/blog/chrome-android-certificate-transparency/ # put your Burp cacert.der in the current working directory! FINGERPRINT=`openssl x509 -in burp_ca_6.cer -inform der -pubkey -noout | openssl pkey -pubin -outform der | openssl dgst -sha256 -binary | openssl enc -base64` echo "chrome --ignore-certificate-errors-spki-list=$FINGERPRINT" > chrome.sh adb push chrome.sh /data/local/tmp/chrome.sh adb shell cp /data/local/tmp/chrome.sh /data/local/chrome-command -line adb shell cp /data/local/tmp/chrome.sh /data/local/android-webview-command -line adb shell cp /data/local/tmp/chrome.sh /data/local/webview-command -line adb shell cp /data/local/tmp/chrome.sh /data/local/content-shell -command -line adb shell chmod 555 /data/local/chrome-command -line adb shell chmod 555 /data/local/android-webview-command -line adb shell chmod 555 /data/local/webview-command -line adb shell chmod 555 /data/local/content-shell -command -line adb shell cp /data/local/tmp/chrome.sh /data/local/tmp/chrome-command -line adb shell cp /data/local/tmp/chrome.sh /data/local/tmp/android-webview-command -line adb shell cp /data/local/tmp/chrome.sh /data/local/tmp/webview-command -line adb shell cp /data/local/tmp/chrome.sh /data/local/tmp/content-shell -command -line adb shell chmod 555 /data/local/tmp/chrome-command -line adb shell chmod 555 /data/local/tmp/android-webview-command -line adb shell chmod 555 /data/local/tmp/webview-command -line adb shell chmod 555 /data/local/tmp/content-shell -command -line adb shell am force-stop com .android.chrome #adb shell am start -a "android.intent.action.VIEW" -d "chrome://version" --es "com.android.browser.application_id" "com.android.chrome" #adb shell am start -n com .android.chrome/com .google.android.apps.chrome.Main -d "chrome://version"
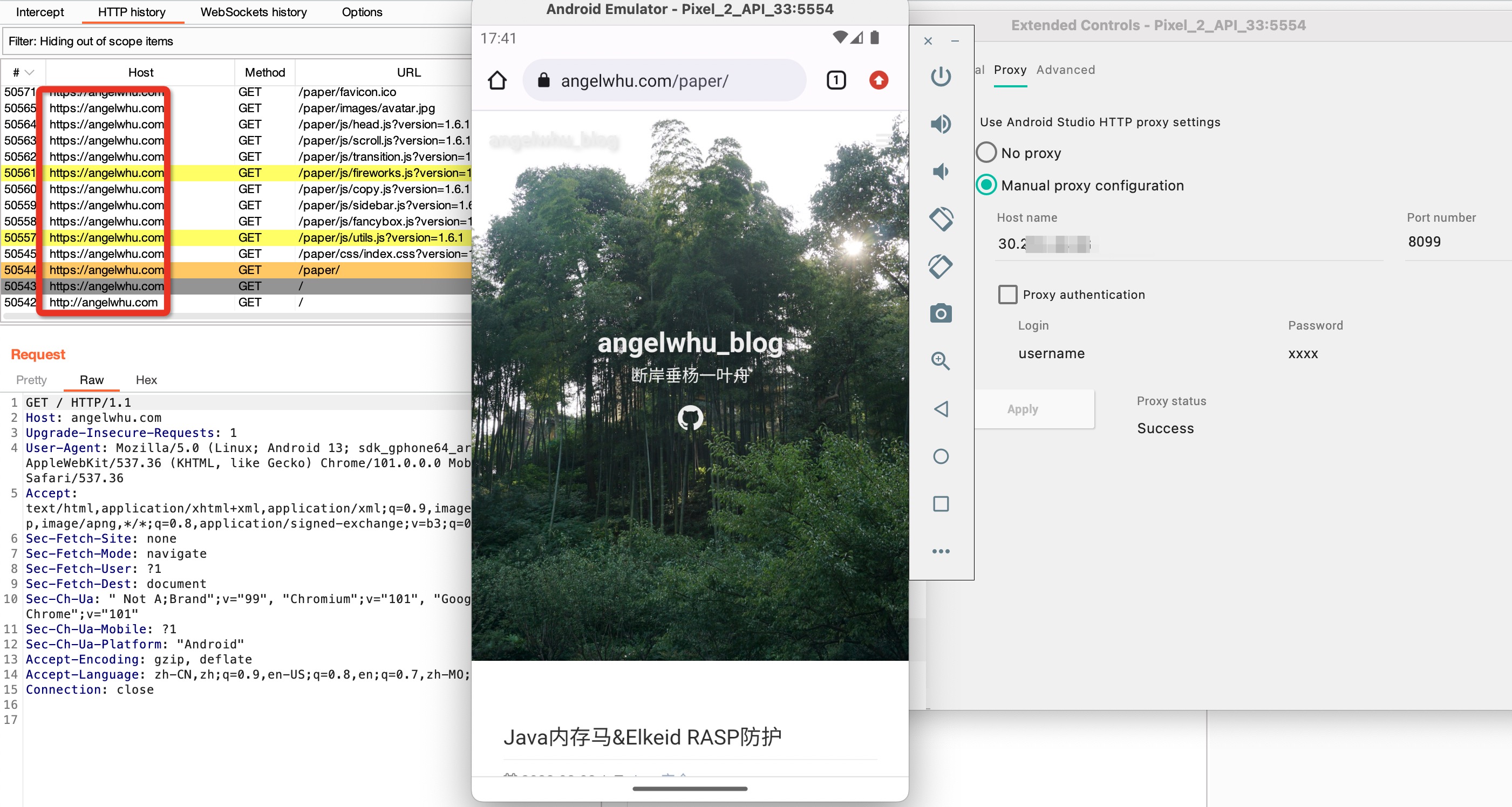
8.Chrome访问Https网站抓包:
0x02 逆向工具
frida版本服务端和客户端要一致,我这边用的frida-server-15.2.2-android-arm64
1 2 3 4 5 6 7 8 pip install frida-tools==11.0 .0 # 对应frida 15.2 .2 获取Android的程序列表: frida-ps -Ua 转发Debug端口: adb forward tcp:27042 tcp:27042 adb forward tcp:27043 tcp:27043
0x03 其他注意
Burp最好重新生成证书
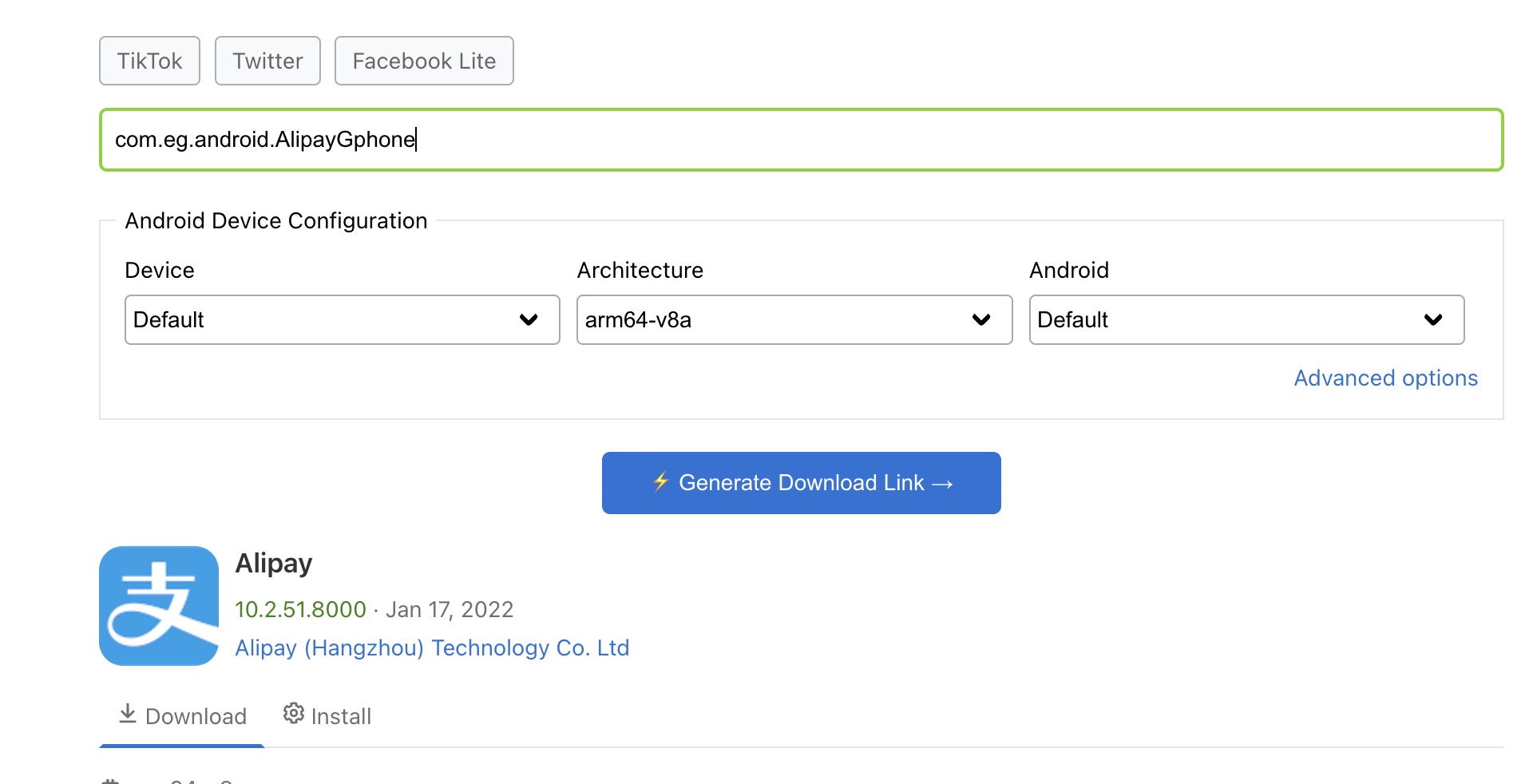
只能安装arm64-v8a架构的APP:使用Chrome插件,apk downloader
0x04 参考